Deploy CrowdStrike Falcon Agent Using Intune
CrowdStrike Falcon is a cloud-native, next-generation antivirus and Endpoint Detection and Response (EDR) solution. It utilizes a single, lightweight agent to protect your infrastructure. In this guide, we will walk through the deployment of the CrowdStrike Falcon Sensor using Microsoft Intune on Azure AD joined devices.
Step 1: Preparation
- Login to the CrowdStrike Portal and download the sensor installer.
- Refer to the official CrowdStrike documentation for detailed download instructions.
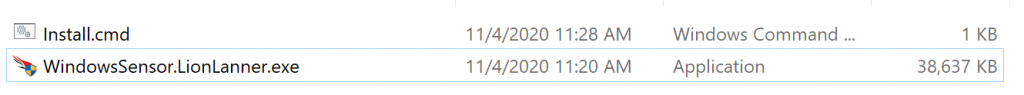
- Place the installer in a dedicated folder (e.g.,
C:\CrowdStrike) and create a file namedInstall.cmd.
The Installation Script
Paste the following code into your Install.cmd file. Ensure you replace the CID with your own Customer ID.
@ECHO OFF
SET ThisScriptsDirectory=%~dp0
WindowsSensor.LionLanner.exe /install /quiet /norestart CID=YOUR_CID_HERECommand Line Switches
| Switch | Description |
|---|---|
| CID= | Customer ID Checksum (Required). |
| /install | Installs the sensor. |
| /quiet | No UI or prompts. |
| /norestart | Prevents forced reboot. |
Step 2: Package the App (Win32)
Use the Microsoft Win32 Content Prep Tool to create the .intunewin file.
.\IntuneWinAppUtil.exe
Source folder: C:\CrowdStrike
Setup file: Install.cmd
Output folder: C:\CrowdStrikeStep 3: Deploy via Intune
- Login to Microsoft Intune Admin Center.
- Go to Apps > All Apps > Add.
- Select Windows app (Win32) and upload your
.intunewinfile.

App Configuration
- Program: Install command:
Install.cmd| Uninstall command:WindowsSensor.LionLanner.exe /uninstall. - Requirements: Operating system architecture:
x64| Minimum OS:Windows 10 1607. - Detection Rule: Manually configure detection rules.
- Rule type: File
- Path:
C:\Program Files\CrowdStrike - File or folder:
CSFalconController.exe
IT Pro Tip: Always test the deployment on a small pilot group of devices before assigning it to the entire "All Devices" group to ensure the CID is active and the sensor communicates correctly with the CrowdStrike console.