Intune Multi Admin Approval: extra layer of security
Last week, attackers used compromised Microsoft Intune credentials to push a mass device wipe across Stryker's endpoints. Hundreds of managed devices were wiped in a single action — no MFA prompt, no second pair of eyes, no friction whatsoever. Just one compromised admin account and a policy that executed instantly.
This is not a novel attack vector. It is a predictable consequence of missing a control that Microsoft ships natively with Intune: Multi Admin Approval (MAA).
The Solution: MAA requires a second administrator to explicitly approve destructive actions before they execute. It takes about 5 minutes to configure. If Stryker had it enabled, the wipe would have sat in an approval queue instead of running.
What Is Intune Multi Admin Approval?
Multi Admin Approval is a built-in Intune governance control that adds a mandatory human approval step to high-impact actions. It directly breaks the single-account compromise attack pattern: even with full admin credentials, an attacker cannot execute a destructive action unilaterally.
What Actions MAA Covers
| Action | Description |
|---|---|
| Device wipe | Factory resets the device, removing all data. |
| Device retire | Removes corporate data and unenrolls the device. |
| Device delete | Removes the device record from Intune. |
| Scripts | PowerShell and shell script deployments. |
| App deployments | Required app assignments pushed to devices. |
Critical caveat: Don't just protect "Wipe". Attackers will use scripts or retire commands if wipe is blocked. Configure all five policy types.
How to Configure Intune MAA
Step-by-Step Guide
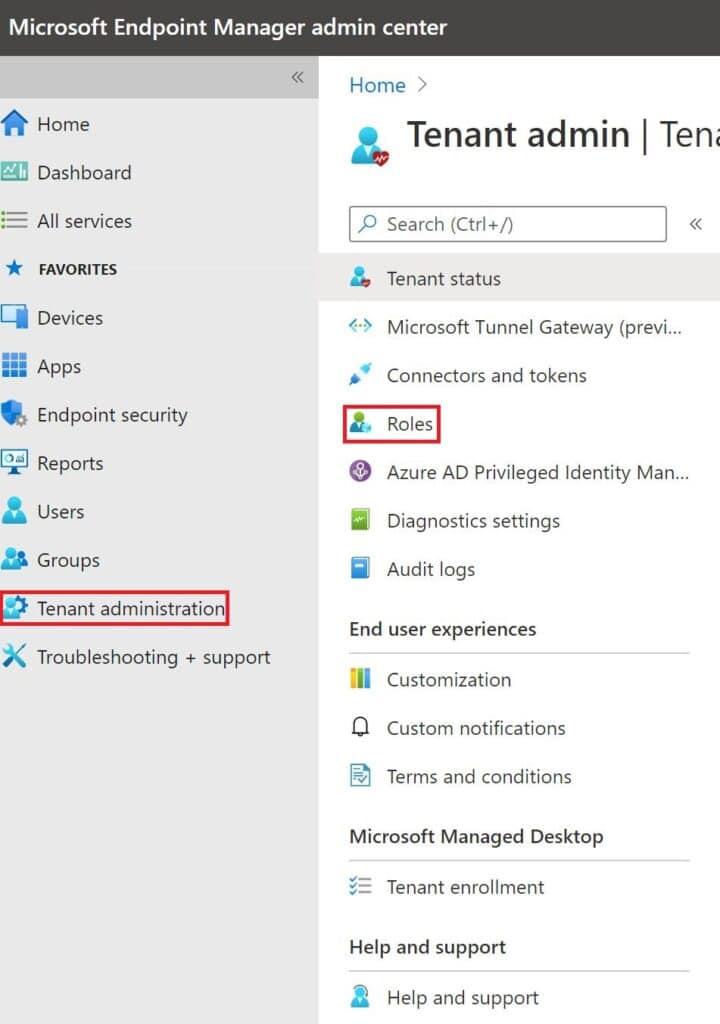
- Navigate: Go to Tenant administration > Multi Admin Approval > Access policies.
- Create Policy: Click + Create. Use a clear name like
MAA - Device Wipe. - Select Type: Under Profile type, select
Device wipe. (Repeat for other types later). - Add Approvers: Select a security group containing your designated approvers.
- Best Practice: Use a dedicated group with at least two members.
- Submit: Enter a business justification and click Submit.
- Final Approval: A second admin must approve this new policy in the Pending approvals tab before it becomes active.
What Happens When MAA Is Active
When an admin initiates a wipe, the action is held. Approvers receive an email and must review the request (Device name, initiator, and justification) in the portal. If denied or ignored, the action is automatically cancelled.
What MAA Does Not Cover
MAA is a strong control but it does not protect everything. It currently excludes:
- Compliance policy changes
- Conditional Access modifications
- Configuration profile deletions
- Bulk operations via Graph API (potential bypass)
Frequently Asked Questions
Does MAA apply to bulk actions?
Yes. If an admin initiates a wipe on multiple devices, the entire batch is held. This is exactly what would have stopped the Stryker attack.
Can I approve my own requests?
No. Self-approval is blocked by Intune logic.
Is it available on my license?
MAA requires Intune Plan 1 (M365 E3/E5, Business Premium, etc.).
Check your configuration against our checklist:
- ✅ Device Wipe, Retire, Delete policies active
- ✅ Scripts and Apps policies active
- ✅ Approver group has 2+ members